If you are running a small business, it can be challenging to decide just how much IT and cybersecurity to invest in. You know that your company and client data need to be secure. You know that hackers are out there. You know that no matter how small your business may be, there is a percent change you will be directly hacked or targeted by roaming malware.
But how much is too much, and what does “Just Right” look like for small business cybersecurity? Today, we’re here to offer a quick overview of the five aspects of cybersecurity that every small business needs.
1) Network Security & Monitoring
First and foremost, every business big or small needs a custom-configured network security stack paired with network monitoring. Your security stack should include a firewall, centralized virus detection, database encryption, and the standard package of security-gap-closing fixes that have been developed over the last 20 years. Any skilled IT security team can help you both set these up and configure them so that the settings are unique to your company needs (and not hackable default settings).
In addition to a security stack, you should also consider network monitoring. Done correctly, network monitoring can throw up very useful red-flags when, say, an employee login is used halfway across the world or when a workstation computer is using a ton of CPU and RAM in the middle of the night when no programs should be running, which indicates lurking malware.
2) Employee Password Protocols
Employee passwords are a subject everyone is tired of, but only because the threat has been ongoing for so long. There are three reasons password security matters and companies are at such a high risk for being infiltrated by a stolen employee login:
- Too-easy passwords can be cracked with brute-force attacks or just by checking the most common passwords
- “123456” “password” and “iloveyou” are all in the top ten most common passwords
- Hackers steal whole databases of passwords from hacked businesses every month
- Most people use just one password for every single account they log into.
Combining points two and three alone create a clear reason why employees need custom, secure passwords for their company logins. This security step is non-optional.
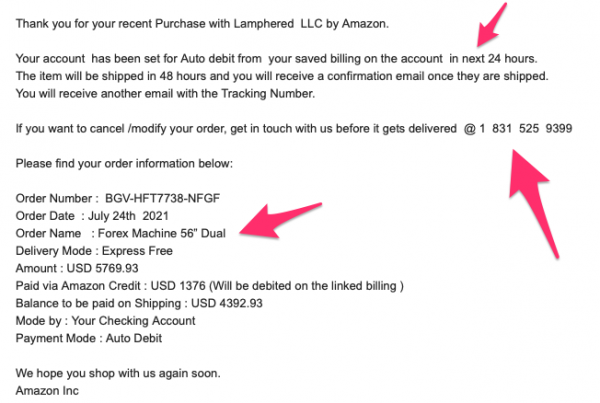
3) Phishing and Whaling Training
Depending on the statistic you’re reading, employees falling for phishing and whaling scams (false emails, phone calls, and chats that convince them to expose sensitive data or open a malware file) account for 50% to 98% of all business hacks. These tactics completely circumvent all your hard work building a security stack.
The best way to protect your business is to train your employees to suspect, identify, avoid, and report phishing and whaling attempts.
4) Backups and Recovery Plans
Comprehensive (all your data, configurations, and servers) backups are a must for any business, no matter the size. There are a large number of reasons why you might have to restore vital files or your entire computer system from a backup after a destructive data-disaster event.
You need backups that have everything you’ll need and a recovery plan that encompasses how you will restore from backups in an emergency.
Just a Few Total-Wipe Risks:
- Network-Wide Ransomware
- Server Host Hack
- Natural Disaster – Flood, Tornado, Earthquake, Hurricane
- Software Update Corruption
5) Penetration Testing (AKA: Cybersecurity Drills)
Finally, the cherry on top of any well-designed cybersecurity defense is penetration testing. What this means is that your IT team (in-house or outsourced) will take the role of hackers and try to see if they can crack your defenses using known hacker methods and their own creative technical expertise. Standard penetration testing reveals weaknesses in your cybersecurity stack that can be quickly patched before they are discovered by a real hacker.
A fun variation of penetration testing is cybersecurity drills, where your IT team poses as hackers in ways that your staff has been trained to identify and report. They will send fake phishing emails and create mock-malware to see if your team remembers their training and knows what to do. Like a fire drill, only for fighting hackers.
—
Does your business need a more complete, customized, or secure cybersecurity solution? Contact us today for a consultation and to explore how we can help you up the cybersecurity defenses of your small business.



Recent Comments